Cloud Security Alliance launched CCZT, the industry-first « Certificate of Competence in Zero Trust »
The Cloud Security Alliance (CSA) is a non-profit organization that focuses on promoting best practices for securing cloud computing environments. It was established in...
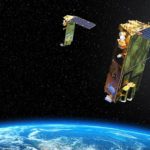
My work about the Viasat attack analysis featured in the Angelina Tsuboi’s course on Satellite Cybersecurity...
I’m very proud and honored to be featured in the Angelina Tsuboi's course on Satellite Cybersecurity Foundations hosted on Udemy. Thank you very much...
ethicallyHackingspace (eHs)® h4ck32n4u75™ (Hackernauts) Community Member
I'm very proud to have been choosen as ethicallyHackingspace(eHs)® h4ck32n4u75™ (Hackernauts) Community Member. Thank's to William Ferguson for this distinction.
The "h4ck32n4u75™" badge, pronounced "hackernauts,"...
Space and Satellites Security Conferences at DEF CON 32 (and a little bit Aviation...
The videos from the Def Con 32 conference held in Las Vegas from August 8th to 11th are now online. Perfect for keeping busy...
Tous les LIVEs pour suivre en direct le premier lancement d’une fusée SpaceX avec...
Ce soir, mercredi 27 mai 2020, l'histoire va se dérouler sous vos yeux. La NASA et SpaceX lancent les astronautes Robert Behnken et Douglas...
Enhancing Threat Understanding: Modeling the Viasat Cyber Attack with MITRE CTID’s Attack Flow Builder
Introduction
In the complex landscape of modern cybersecurity, understanding the intricate mechanisms of sophisticated cyber attacks has become paramount.
On February 24, 2022, Viasat, a global...
Mettez-vous dans la peau des astronautes de la NASA avec ce simulateur pour vous...
Mettez-vous dans la peau d’un astronaute de la NASA et essayez de vous amarrer à l’ISS avec ce simulateur de la capsule Crew Dragon....
Very proud to have earned the Kelley School of Business – Space Cybersecurity Professional...
I’m pleased to announce that I have obtained a new certification: Kelley School of Business Executive Education Space Cybersecurity from Indiana University - Kelley...
ATT&CK v13 released with significant updates : Pseudocode, Swifter Search, Mobile Data Sources and...
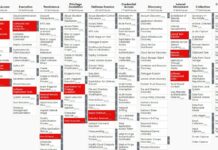
🔥 On Tuesday 25 April 2023, the MITRE Corporation released ATT&CK v13, the new version of its framework.
This new version includes significant updates and...
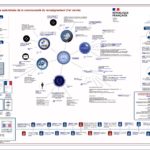
An analysis of the Viasat cyber attack with the MITRE ATT&CK® framework
Disclaimer
To do this analysis of the Viasat cyber attack, I used the open-source intelligence (1) of the team composed by Nicolò Boschetti (Cornell University),...