Coverage by CyberInflight of the Russian satellite telecom Dozor-Teleport Attack
CyberInflight (www.cyberinflight.com) is an independant consulting and business intelligence company dedicated to the topic of Aerospace Cybersecurity. CyberInflight’s goal is to raise the global cybersecurity...
A comprehensive 3-day Space Domain Cybersecurity course organized around the SPAce Domain Cybersecurity (SpaDoCs)...
This article describes a comprehensive 3-day Space Domain Cybersecurity course organized around the SPAce Domain Cybersecurity (SpaDoCs) Framework.
Course Description
This Space Domain Cybersecurity course examines...
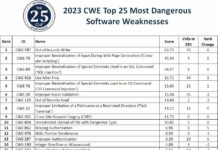
Top 25 most dangerous software weaknesses than can affect satellites in 2023
Issues of vulnerabilities of space systems to cyber attacks has long been ignored for reasons common to industrial systems or SCADA (Supervisory Control And...
🌠🛰️ Space Cybersecurity Watch by CyberInflight, W23 – 2023
CyberInflight and Florent Rizzo released a new 🌠🛰️ Space Cybersecurity Weekly Watch 🛰️🌠 for Week 23 (May 30 - June 5, 2023). The team consolidates...
Sample of the last Space Cybersecurity Market Intelligence 2023 Report from CyberInflight
CyberInflight and Florent Rizzo shared an excerpt of their last Space Cybersecurity Market Intelligence 2023 Report.
Here is what Florent said in French about this...
A quick comparaison of recently released Cybersecurity Frameworks for Space Sector
« The space sector is in need of frameworks and methodologies specific to our unique operating environment » said Gregory Falco (Aerospace Security & Space Technology Asst. Prof...
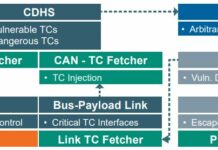
An analysis of the Thales satellite hacking demo CYSAT 2023 by SPARTA team
Brandon Bailey & Brad Roeher from the SPARTA team analyzed, in this article, Thales Group’s CYSAT ’23 presentation material to deconstruct the experiment, extract lessons...
Space Odyssey: An Experimental Software Security Analysis of Satellites
The abstact below is taken from a paper written by Johannes Willbold, Moritz Schloegel, Manuel Vogele, Maximilian Gerhardt, Thorsten Holz and Ali Abbasi.
This paper...
CYSAT ’23, a space cybersecurity conference : Full Keynotes and Presentations
CYSAT ’23 is the first conference in Europe dedicated to satellite and space industry cyber security. It took place from 26 to 27 April...
MITRE Caldera™ for OT enables red teams and blue teams to run automated adversary...
MITRE CALDERA is a framework for automating cyber defense testing. CALDERA is developed by the MITRE Corporation, a nonprofit organization based in the United...