Space and Satellites Security Conferences at DEF CON 32 (and a little bit Aviation...
The videos from the Def Con 32 conference held in Las Vegas from August 8th to 11th are now online. Perfect for keeping busy...
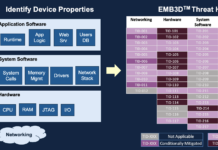
MITRE Releases EMB3D™ – A Cybersecurity Threat Model for Embedded Devices
Collaborative framework provides common understanding to mitigate cyber threats to critical infrastructure
MCLEAN, Va. & BEDFORD, Mass., May 13, 2024--(BUSINESS WIRE)--The EMB3D Threat Model is...
Hacktivism Goes Orbital: Investigating NB65’s Breach of ROSCOSMOS
In March of 2022, Network battalion 65 (NB65), a hacktivist affiliate of Anonymous, publicly asserted its successful breach of ROSCOSMOS’s satellite imaging capabilities in...
“Space Cybersecurity” magazine special edition from PenTest and Hakin9
PenTest and Hakin9 are very proud to present with a special edition, created in a collaborative process between experts in the field of space...
“Introduction to Cybersecurity in Space Systems” with Tim Fowler is coming up during the...
Tim Fowler will provide a training course called "Introduction to Cybersecurity in Space Systems" at "The Most Offensive Con that Ever Offensived – Bypass...
[Book] The Battle Beyond: Fighting and Winning the Coming War in Space
Fundamentally, Paul Szymanski and Jerry Drew remind us that--more than just simply a clash of weapons--all warfare manifests as a competition between human minds....
Cloud Security Alliance launched CCZT, the industry-first “Certificate of Competence in Zero Trust”
The Cloud Security Alliance (CSA) is a non-profit organization that focuses on promoting best practices for securing cloud computing environments. It was established in...
Very proud to have earned the Kelley School of Business – Space Cybersecurity Professional...
I’m pleased to announce that I have obtained a new certification: Kelley School of Business Executive Education Space Cybersecurity from Indiana University - Kelley...
Detecting Aircraft Spoofing With Fly-Catcher
Aviation technology is vulnerable to a wide range of cyber threats. Hackers can easily spoof "ghost" aircraft into the sky.
In order to tackle this...
L’Aéro Recrute, un nouveau programme dont je suis Ambassadeur : Pour mettre en avant...
Je suis fier de rejoindre le programme L'Aéro Recrute. Je suis nommé Ambassadeur pour la filière Aéronautique et Spatiale.
A ce titre, vous pouvez me...





![[Book] The Battle Beyond: Fighting and Winning the Coming War in Space](https://www.spacesecurity.info/wp-content/uploads/2023/12/The-Battle-Beyond-Fighting-and-Winning-the-Coming-War-in-Space-218x150.jpg)
















